-
John Daghita was arrested on allegations of siphoning $40M+ from government crypto seizure addresses.
-
The suspect allegedly gained access to the digital assets through his father’s company while contracted by the US government.
-
The grand theft is one among many similar schemes running rampant in the crypto industry.
John Daghita, aka Lick, was arrested today by the Federal Bureau of Investigation (FBI) in the Caribbean for allegedly stealing $46 million worth of seized crypto assets from the US Marshals Service (USMS).
Suspect arrested for $46M grand crypto theft
The heist began in 2024, when Command Services & Support, Inc. (CMDSS), a technology company, was awarded a contract to handle asset disposal for the US Department of Justice (DoJ) and the Department of Defense (DoD). Dean Daghita was head of the company while his son John worked as an employee.
Per the ZachXBT (revealer of the Axiom insider trading) expose, John allegedly used his status to withdraw confiscated cryptocurrencies to his personal wallets.
He remained anonymous until January 23, 2026, when he decided to flaunt his success to another confessed thief by the name of Dritan Kapplani Jr.
A recording of this interaction shows how John revealed his wallet address, which ZachXBT then linked to several scams and a US Government address from which digital assets had been siphoned in 2024.
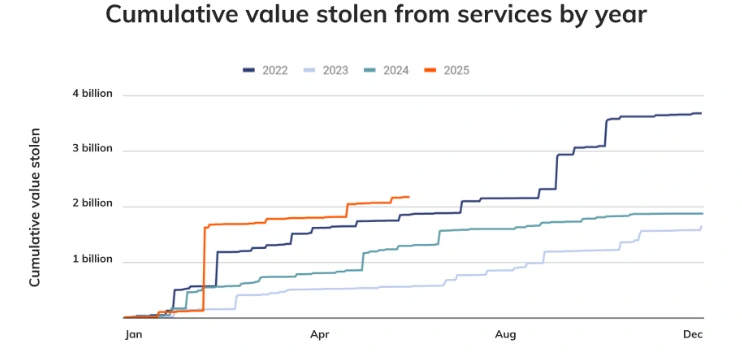
Source: Chainalysis
This year, Apple cautioned iOS users of the “Coruna” exploit, which hunts for crypto wallet seed phrases in phones running iOS 13.0 through 17.2.1, but not later (iOS 18+). The malware is estimated to have affected at least 42,000 devices.
More recently, South Korea’s tax agency mistakenly revealed its virtual asset wallet seed phrase online, leading to the loss of $4.8 million worth of tokens.
 coinpedia.org
coinpedia.org
