North Korea has turned crypto theft into something resembling a nationalized industry. And business is booming.
A new report from blockchain security firm CertiK attributes roughly $2.06 billion of the $3.4 billion lost to crypto hacks in 2025 to groups linked to the Democratic People’s Republic of Korea. That’s 60% of the entire industry’s security losses for the year, spread across just 79 of 656 documented incidents.
Put differently, DPRK-linked hackers accounted for 12% of all reported attacks but walked away with the majority of the money.
The numbers keep getting worse
CertiK’s Skynet DPRK Crypto Threats Report, shared with Cointelegraph on Tuesday, paints a picture of escalating sophistication. Between 2016 and early 2026, North Korean hacking groups stole approximately $6.75 billion in digital assets across 263 incidents. CertiK itself notes that figure is likely understated.
And 2026 isn’t starting any better. So far this year, DPRK hackers have already claimed $620.9 million of the $1.1 billion in crypto losses reported, led by a $291 million exploit targeting KelpDAO.
The proceeds are funneled directly into funding North Korea’s nuclear and ballistic missile programs. Crypto theft has become, in CertiK’s assessment, a state-managed revenue source operating at an unprecedented scale.
From phishing emails to fake employees
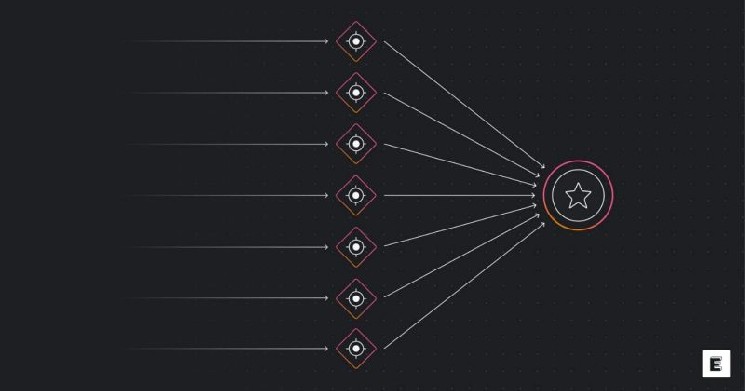
CertiK identifies a clear shift toward social engineering, supply chain attacks, and physical infiltration. DPRK operatives are reportedly embedding themselves inside target organizations, posing as legitimate employees or contractors to gain insider access.
The Bybit hack provides a case study in how quickly stolen funds can be moved once the initial breach succeeds. According to the report, 86% of the $ETH stolen in that incident was laundered into $BTC in under a month. The conversion happened through a combination of mixers and exchanges, making recovery extraordinarily difficult.
What this means for the industry
Of the 656 incidents CertiK documented in 2025, the 79 attributed to North Korea accounted for the lion’s share of dollar losses. This suggests that the biggest vulnerability isn’t the sheer number of exploits. It’s the sophistication of the most dangerous actors.
For DeFi protocols, the infiltration angle changes the threat model entirely. Code audits and bug bounties address technical vulnerabilities. They don’t catch a state-sponsored operative who passed your hiring process and now has access to internal systems.
Converting 86% of a massive $ETH haul into $BTC within weeks suggests well-established pipelines that can absorb large volumes without significant slippage or detection.
 cryptobriefing.com
cryptobriefing.com