World Liberty Financial’s ($WLFI) governance tokenholders are being hit with a known phishing wallet exploit using Ethereum’s EIP-7702 upgrade, SlowMist founder Yu Xian says.
Ethereum's Pectra upgrade in May introduced EIP-7702, which allows external accounts to temporarily act like smart contract wallets, delegating execution rights and allowing batch transactions, which are aimed at streamlining a user’s experience.
Xian said in an X post on Monday that hackers are exploiting the upgrade to pre-plant a hacker-controlled address in victim wallets, then, when a deposit is made, they quickly “snatch” the tokens, which in this case, is affecting $WLFI tokenholders.
“Encountered another player whose multiple addresses’ $WLFI were all stolen. Looking at the theft method, it’s again the exploitation of the 7702 delegate malicious contract, with the prerequisite being private key leakage,” Xian said.

The Donald Trump–backed World Liberty Financial ($WLFI) token began trading Monday morning, with a total supply of 24.66 billion tokens.
How it works
In the lead-up to the official launch, an X user reported on Aug. 31 that a friend had their $WLFI tokens drained after transferring Ether ($ETH) into their wallet.
In a reply, Xian said it was clearly an example of the “Classic EIP-7702 phishing exploit,” where the private key was leaked, and the bad actor then pre-plants a delegate smart contract into the victim’s wallet address connected to the key.
In a previous post, Xian said the private keys are usually stolen through phishing.
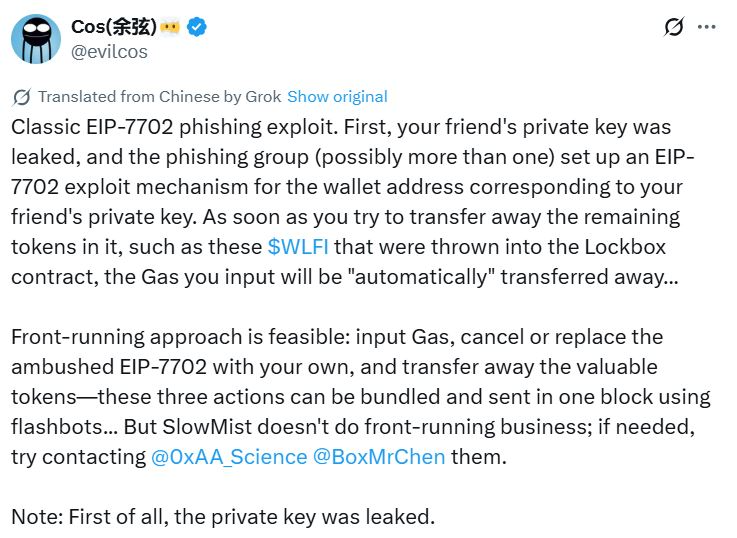
“As soon as you try to transfer away the remaining tokens in it, such as these $WLFI that were thrown into the Lockbox contract, the gas you input will be automatically transferred away,” he said.
Xian suggested to “cancel or replace the ambushed EIP-7702 with your own,” and transferring away tokens from the compromised wallet as a possible solution.
Crypto users discuss thefts on $WLFI forums
Some have been reporting similar issues in the $WLFI forums. One posting under the handle hakanemiratlas said his wallet was hacked in October last year and now worries his $WLFI tokens are at risk.
“I managed to transfer only 20% of my $WLFI tokens to a new wallet, but it was a stressful race against the hacker. Even sending $ETH for gas fees felt dangerous, since it could have been stolen instantly as well,” they said.
“Currently, 80% of my $WLFI tokens are still stuck in the compromised wallet. I am extremely worried that once they unlock, the hacker might immediately transfer them away.”
Another user under the handle Anton said many other people are facing a similar issue because of how the token drop was implemented. The wallet used to join the $WLFI whitelist needs to be used to participate in the presale.
“The instant the tokens arrive, they will be stolen by automated sweeper bots before we have a chance to move them to a secure wallet,” he said.
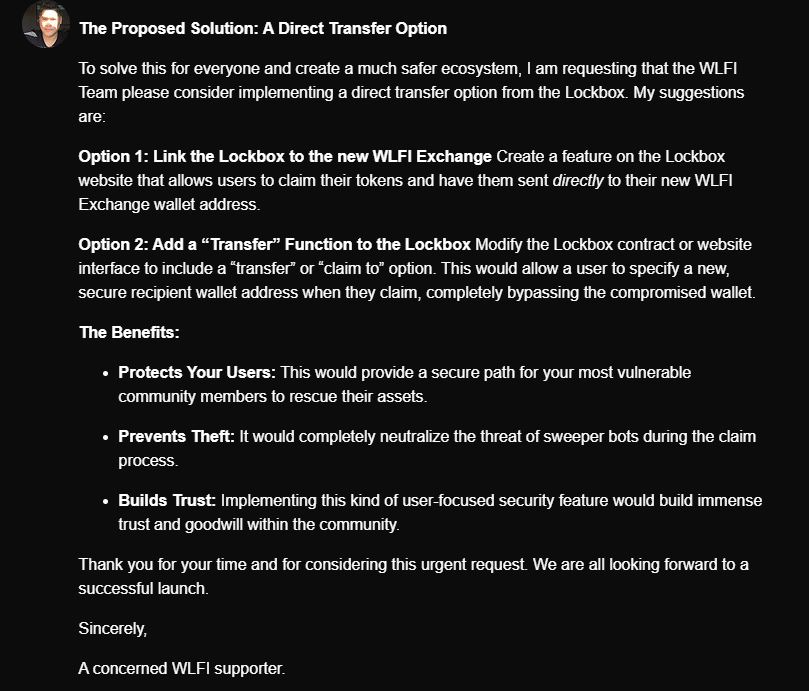
Anton is also requesting the $WLFI Team to consider implementing a direct transfer option for the tokens.
Scammers targeting token launch
Numerous $WLFI scams have appeared in the lead-up and post token launch. Analytics firm Bubblemaps identified several “bundled clones” look-alike smart contracts that imitate established crypto projects.
Meanwhile, the $WLFI team has warned that it doesn’t contact via direct message on any platform, with the only official support channels through email.
“If you receive a DM claiming to be from us, it is fraudulent and should be ignored. If you receive an email, always double-check that it is coming from one of these official domains before responding,” the $WLFI team said.
 cointelegraph.com
cointelegraph.com
