They say code is law in the crypto space. Turns out, code is also money for white hat hackers.
Hackers who find themselves at discovery of a severe bug in crypto infrastructure must decide: Do they exploit the bug (black hat) or report it (white hat)? A gray hat might go either way depending on how they feel about the target.
Famous modern black hats include state-sponsored hackers like the Lazarus Group — who among their numerous attributed misdeeds includes raiding the Axie Infinite token bridge, Ronin, for $625 million in crypto in 2022.
White hats earn far less through crypto bounty programs but it’s not chump change. About 60 companies working with digital assets and blockchain have public programs on crowd-sourcing cybersecurity platform HackerOne.
In that time, crypto-related firms dished out more than $640,000 to hackers who’d discovered and reported vulnerabilities in their projects rather than exploit them.
Read more: Security review competition will offer a bounty of $1.2M
Many were launched in the past year or so, including campaigns from derivatives exchange Bybit, Bored Apes creator Yuga Labs and the DAO stewarding development of the Tron blockchain.
NFT marketplace Magic Eden led the group with $83,000, split between 15 different payouts. Nearly half fetched $10,000 a pop, the figure attributed to “critical” bugs of the highest severity, although no details for any have been disclosed so far (Magic Eden did not respond to request for comment).
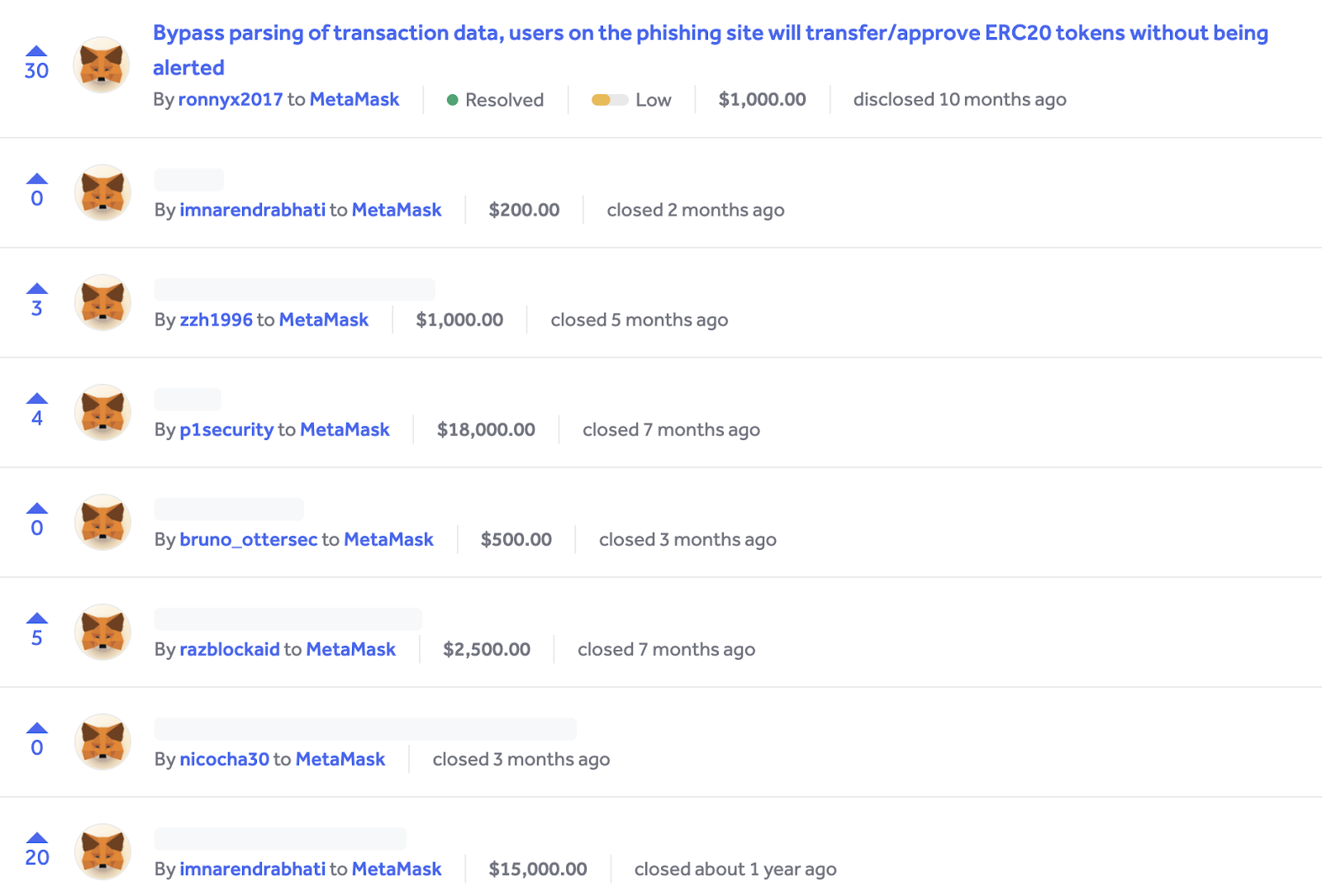
Browser-based, self-custody crypto wallet MetaMask came a close second with payouts totalling $75,750, followed by Hedera Hashgraph, the firm behind layer-1 network Hedera, with $67,200.
Those figures only reflect publicly disclosed payouts, so the actual cash value of the bug bounties would actually be higher. Bug bounties don’t have to be public, either, and can be run completely in private.
MetaMask, which says it has more than 30 million users, is one of the cornerstones of the Consensys product suite focused on Ethereum (Consensys was founded by Ethereum co-founder Joe Lubin). MetaMask aims to provide an intuitive and safe way to use cryptocurrency and otherwise interact with blockchain platforms.
“We conduct thorough audits, but it’s equally crucial for us to operate bug bounty programs to maintain a perpetual vigilance over time,” Nicholas Ellul, manager of security engineering at MetaMask, told Blockworks.
“This approach enhances our awareness of potential risks, enables us to devise mitigation strategies and contributes to developing the industry’s most secure wallet.”
Programs like its HackerOne campaign also help decentralize the software auditing process, he explained. The firm effectively invites hackers around the world to contribute and be rewarded for helping safeguard its users.
Coinbase will pay $1 million to anyone who can hack its users
Crypto-related companies over the past year altogether reported awarding around 650 bounties to those who reported bugs over exploiting them. And of those, 499 were accompanied with details of how much each hacker earned.
Major US crypto exchange Coinbase paid out 120 individual bug bounties, more than any other company. Of the bounties with disclosed cash prizes, all were paid at either low or medium severity.
Coinbase hasn’t disclosed details of any vulnerabilities discovered through its HackerOne campaigns since March 2018, when it awarded $20,000 to the researcher who’d figured out how to credit themselves ether (ETH) that they didn’t have, but it has given detailed information at times through its blog.
The Delaware-registered firm has updated its bug bounty program since then. Coinbase now offers up to $1 million to anyone who can cause “serious business disruption” to the platform, including “unauthorized access to Coinbase owned hot/cold wallet assets,funds and/or wallet private keys.”
This is considered “extreme” severity, which is worse than “critical.” Low severity these days means bugs that lead from anywhere to “financial loss of less than $100,000 for any Coinbase owned system to maliciously tinkering with non-critical systems and data (about 10% of all bounties awarded over the past year were paid at either high or critical price points).
“Coinbase takes the security of its products, services and customers very seriously,” a spokesperson told Blockworks. “The money spent for bug bounties and software audits should be viewed as complementary in nature.”
They added: “Crowdsourcing talent through bug bounty platforms enables Coinbase to leverage talent from around the world with varying levels of experience and expertise who can provide feedback and report findings that are relevant to geolocation.”
Coinbase particularly considers disclosing novel bugs from which the security community could learn, to the benefit of the broader industry.
Brave Software, the San Francisco startup behind the crypto-centric Brave web browser, meanwhile regularly publishes extensive details of the bugs that hackers find.
Eight months ago, one high severity vulnerability in Brave’s QR code scanner “allowed attackers to direct users to malicious sites without their consent or knowledge.”
“This vulnerability put the security of Brave users at risk and allowed them to be exposed to phishing and malware attacks.” The dollar figure attached to the bounty wasn’t disclosed.
“We believe in transparency and feel there is little downside to disclosing details once a bug is fixed and the fix is widely available, as it creates greater trust in Brave and helps other security researchers in their work,” Yan Zhu, chief information security officer at Brave, told Blockworks.
The overall average for bounties paid in the past year across the entire set of companies with active programs works out to be under $1,300.
Read more: LayerZero, Immunefi offer bug bounty with $15M max payout
Brave over the past year or so has paid out at least $18,000 through its HackerOne program, averaging less than $1,000 per bounty (if only calculating only the ones that are disclosed, which include two critical bugs and eight with high severity).
Zhu said Brave spends less per valid bug on HackerOne compared to third-party audits. “It’s greatly helped us have confidence in our products’ security.”
Offer hackers money and they will come
Hedera Hashgraph doled out $67,200 through its program across nine disclosures, three high and one critical. Details weren’t disclosed.
Read more: Bribing hackers seems to work: 3 hacks returned in 3 months
Hedera is a smart contract network which has its own stablecoins, NFT platforms, decentralized exchanges and lending protocols, although its $78-million total value locked puts it further down the list.
Still, the market capitalization of its native token HBAR is $2.56 billion, ahead of Ethereum layer-2 Arbitrum.
The scope of Hedera’s bounty offering includes code run by Hedera consensus nodes and software development kits — the raw guts of the blockchain.
Like all blockchains, any truly significant vulnerabilities in Hedera’s underlying software, like avenues to double-spend or shut transactions down through consensus failures, potentially threaten the value of all cryptocurrencies on the network, including HBAR.
Joe Blanchard, chief information security officer for Hedera development studio Swirlds Labs, explained that traditional audits are more structured assessments made at a particular time at a fixed price. Bug bounties are an entirely different beast.
“We see these two as being complementary with bug bounties generally being more tactical, while more traditional audits tend to be more strategic and are conducted on a scheduled tempo or occasionally on an as-needed basis directly tied to the active projects and their development tempo,” he said.
“Bug bounty programs on the other hand are ongoing with no time limits and pay only upon provable results. Informational findings don’t cut it.” (MetaMask’s Ellul noted that bounty programs still require continual upkeep and maintenance from their own security team.)
Blanchard said the team had focused on developing relationships with the developer community, resulting in increased attention to Hedera’s code.
This “exposed some issues in our code bases and architecture [and gave further insight] into hardening the network not only for the specific defect, but also to proactively address similar issues in the future,” he said.
“Many of the white hats participating have provided an interesting perspective on the kinds of potential vulnerabilities they are identifying and different paths to mitigation…Bugs by their nature expose defects which may include risks and exposure paths into our network.”
And even though disclosing details of resolved vulnerabilities would boost transparency, Blanchard said Hedera doesn’t see value in “giving attackers ideas for vectors that our or other peoples’ software can be made vulnerable.”
MetaMask and Consensys also opt to disclose details of bugs here and there. One medium severity report from November 2022, but disclosed the following July, showed that attackers were able to deep-link into the in-browser app and force the target machine to download a file — which could potentially be malicious.
A dollar figure wasn’t revealed for that particular bounty but its policy notes that medium severity bugs carry a $2,500 cash prize.
“Transparency is a core value at Consensys and MetaMask,” Ellul said. “When a vulnerability is discovered, and we wish to encourage more people to find similar vulnerabilities, we always opt for disclosure.”
Exceptions include when vulnerabilities may be common to other wallets, in which case they would delay revealing details, and instances where users could be at risk. “Our ultimate goal is Web3 users’ safety.”
 blockworks.co
blockworks.co