An anonymous white hat hacker has published a detailed report alleging that the DeFi protocol, SushiSwap, currently features a vulnerability that puts at least a billion dollars worth of user funds at risk.
An effort to get SushiSwap developers to confidentially fix the bug has failed, leading up to the decision to make the information publicly available.
According to the hacker, the motive is to “educate current and future SushiSwap users of the risks they are taking by trusting these vulnerable contracts […] and point out to white hat hackers how SushiSwap casually handled this matter being brought to their attention.”
The SushiSwap Vulnerability
The white hat hacker reportedly noted that there is a “vulnerability within the emergencyWithdraw function in two of SushiSwap’s contracts, MasterChefV2 and MiniChefV2.” These contracts are in charge of SushiSwap’s 2x reward farms, and SushiSwap pools on sidechains such as Binance Smart Chain, Polygon, Factom, Avalanche etc.
For the basics, an emergency withdrawal function is a safety net prominently featured across DeFi protocols, including SushiSwap’s Ethereum smart contracts. This feature allows users to withdraw their Liquidity Provider (LP) tokens in the event of an emergency, potentially forfeiting any rewards earned until that point.
While both SushiSwap contracts include this feature, the hacker claims that it is misleading and doesn’t work as intended. SushiSwap’s comment on the code shows that the emergency withdrawal function should allow users to withdraw funds without caring about rewards. However, the function fails if there are no rewards within the SushiSwap pool.
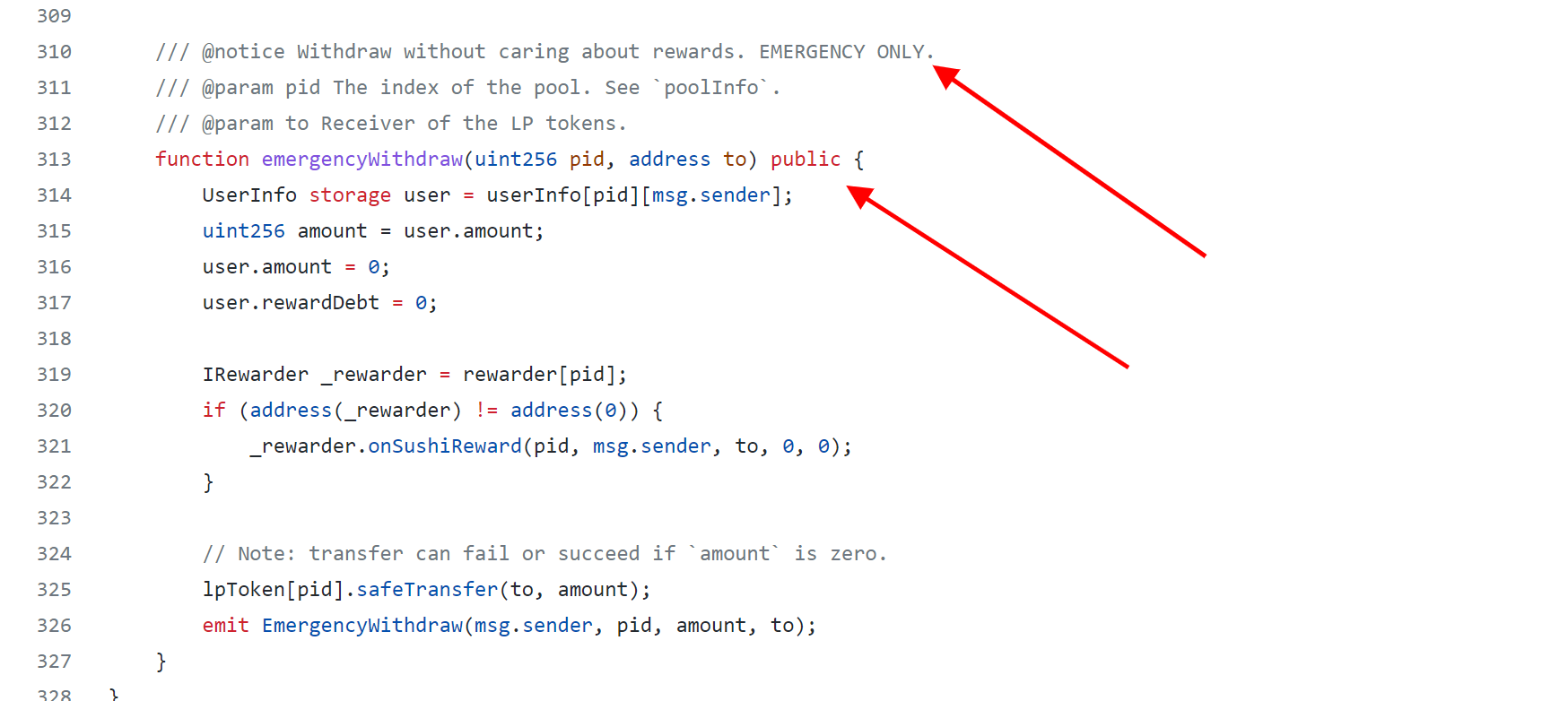
(SushiSwap MasterChefV2 via Github)
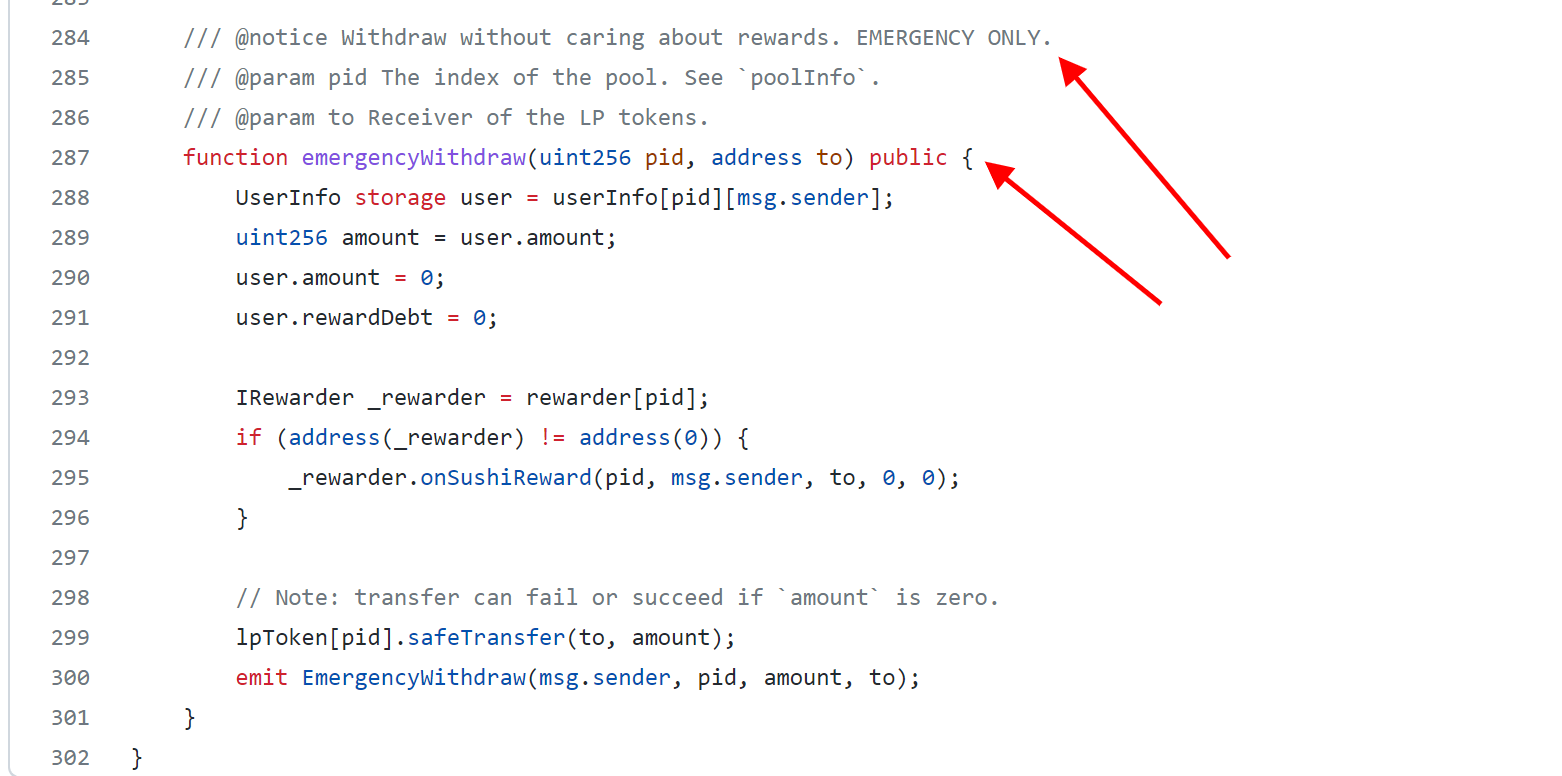
(SushiSwap MiniChefV2 via Github)
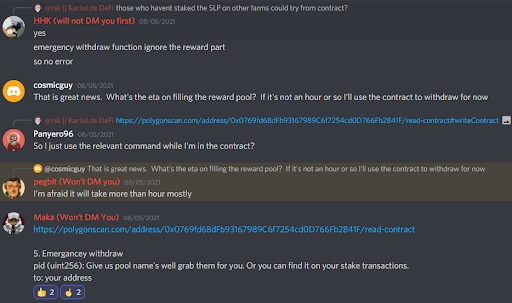
According to the report, the token rewards that SushiSwap pays out to LP token holders are stored in a different account. Sometimes the rewards dry up and must be filled manually by the project’s team using a multi-signature account with developers apparently in different time zones.
“It can take approximately 10 hours for all signature holders to consent to refilling the rewards account, and some reward pools are empty multiple times a month,” the report claims.
During this period, SushiSwap LP providers cannot “stake, unstake, collect rewards or even make use of the emergency withdrawal function.” This lockup means that user funds are practically held hostage during this period, making it impossible for them to react to price movement in the staked LP tokens.
“SushiSwap’s non-Ethereum deployments and 2x rewards (all using the vulnerable MiniChefV2 and MasterChefV2 contracts) hold over $1 billion in total value. This means that this value is essentially untouchable for 10-hours several times a month.“
The hacker also notes that SushiSwap’s Discord support team would often encourage users to call the emergency withdrawal function. Since the call would normally fail because of the vulnerability, users must remain patient until whenever the reward pools are refilled.
Aside from not being able to withdraw funds in a highly volatile market, the hacker claims the vulnerability could be exploited by a SushiSwap competitor with bad intent. Using a large amount of LP tokens, they can incessantly dry out the multiple reward pools and thus hold the funds of other users hostage until whenever the team is able refill the pool.
SushiSwap’s Response to Vulnerability
Following the discovery of the vulnerability, the white hat hacker claimed they confidentially reached out to SushiSwap to report the bug. The project referred the hacker to Immuefi, a bug bounty platform where Sushiswap listed their bug bounty program.
SushiSwap has a $1.25 million maximum bounty posted on Immunefi, with hackers that disclose high-risk vulnerability eligible for a payout of up to $40,000. However, in this case SushiSwap closed the issue without paying the bounty and also not fixing the vulnerability.
The team allegedly stated that “the operational issue in question was known at the time of implementation. No fix has been done other than transferring additional funds.”
As per the hacker, the statement implies that SushiSwap “intentionally and purposefully introduced a vulnerability that could lock up and cost users millions of dollars, [and also] they refuse to fix it.”
Coinfomania reached out to SushiSwap for comment regarding the alleged vulnerability, but did not receive a reply.
 coinfomania.com
coinfomania.com