It should come as no surprise that a noticeable increase in the number of threats and attacks that target crypto or leverage them has coincided with the sharp surge in the market capitalization of cryptocurrencies.
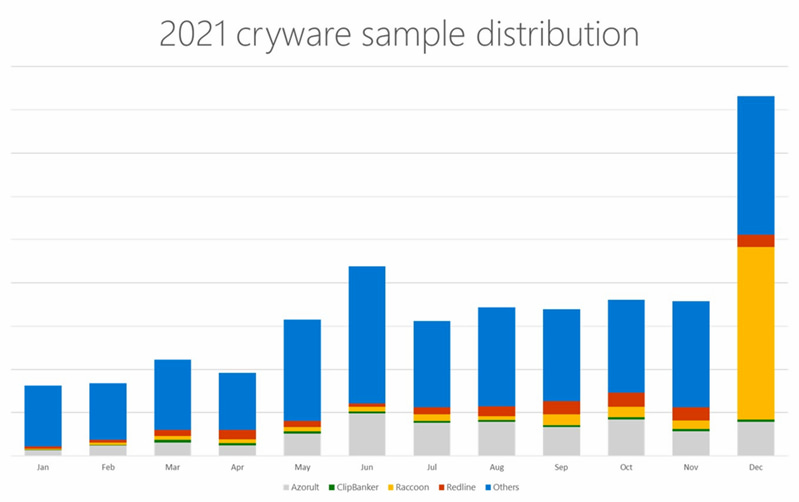
In particular, Microsoft (NASDAQ: MSFT) researchers are seeing an increase in related malware and techniques, as well as a new threat called ‘Cryware,’ according to a new security blog post published by the company on May 17.
Cryware is a kind of data stealer that targets non-custodial crypto wallets (hot wallets). Since hot wallets, in contrast to cold wallets, are kept locally on a device and give simpler access to the cryptographic keys that are required to complete transactions, an increasing number of threats are focusing their attention on them.
Berman Enconado and Laurie Kirk from the Microsoft 365 Defender Analysis Workforce stated in the report.
“With the growing popularity of cryptocurrency, the impact of cryware threats have become more significant. We’ve already observed campaigns that previously deployed ransomware now using cryware to steal cryptocurrency funds directly from a targeted device.”
The role of crypto in attacks has changed
Prior to the development of cryware, the function of cryptocurrencies during an attack or the stage of an assault in which they were involved varied depending on the overall purpose of the attacker. As an example, several ransomware attacks favor the use of cryptocurrencies as a form of ransom payment.
Nevertheless, in such a case, the target user will need to carry out the transfer on their own. In the meanwhile, cryptojackers, which are one of the most common types of malware connected to cryptocurrencies, do attempt to mine crypto on their own, however the success of such a strategy is strongly reliant on the resources and capabilities of the targeted system.
Cryware allows attackers to instantly move the target’s cryptocurrency to their own wallets after gaining access to their hot wallet data. Blockchain transactions are final even if performed without a user’s agreement or knowledge. Unlike credit cards and other financial transactions, there are no methods to reverse or protect consumers against fraudulent crypto transactions.
Regular expressions (regexes) may be used to locate hot wallet data like as private keys, seed phrases, and wallet addresses, using these patterns, cryware automates the procedure. Clipping and switching, memory dumping, phishing, and frauds are all methods used to acquire wallet information.
 finbold.com
finbold.com