This post is a guest post by cross-chain bridge and interoperability platform Wanchain. You will see our editor comments in brackets [like these].
In a recent post on Reddit, Ethereum (ETH) co-founder Vitalik Buterin published his concerns regarding the security of cross-chain applications. His concerns stem from an alleged fundamental security limitation inherent to cross-chain bridges. Security is undoubtedly one of the most important factors blockchain platforms and decentralised applications must consider. In this article, the Wanchain R&D team, builders of the world’s premier decentralised blockchain interoperability solution, analyse Mr. Buterin’s claims and present their thoughts on cross-chain security.
Dissecting Vitalik’s argument: “blockchains maintain many of their guarantees even after a 51% attack”?
Vitalik’s argument centers around the impact of a 51% attack. He claims that, while blockchains “maintain many of their guarantees even after a 51% attack,” cross-chain bridges open the possibility for the attacker to steal funds by moving tokens onto another chain. To understand this reasoning, it is helpful to first describe a 51% attack.
What is a 51% Attack?
A 51% attack occurs when a single person or group gains control of more than 50% of the hashing power in a proof of work (POW) consensus blockchain or more than 50% of the total stake in a proof of stake (POS) blockchain. When attackers gain control over a blockchain using a 51% attack, they can reject valid proposed blocks or revert valid blocks that have yet to be finalized.
Central to Mr. Buterin’s argument is the fact that a 51% attack is not able to alter user transactions and cannot revert blocks finalized before the attack. In other words, the guarantee of the immutability of the blockchain is up to the block where the 51% attack took place. This is all true. However, the word “many” is doing some heavy lifting in Mr. Buterin’s argument, as blocks, transactions, and assets sent after the commencement of the 51% attack are not guaranteed.
[Editor’s Note: For those concerned about 51% attacks, this helps make a good argument for interoperability chains generally. Cosmos with their IBC and especially Polkadot with its relay chain provide an added layer of security while keeping all the transactions within one ecosystem.]
We show you this scenario in Figure 1, below.
The Impact of a 51% Attack on A Blockchain
Let’s dissect the impact of a 51% attack using Figure 1:
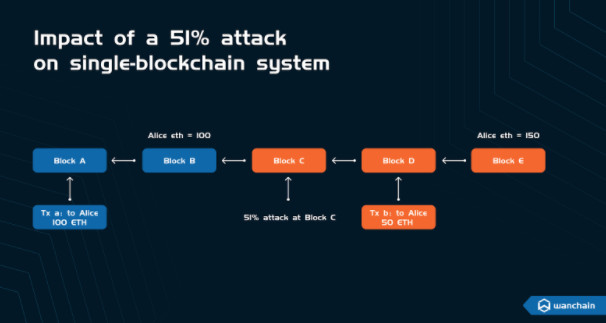
- A regular transaction of 100 ETH, Tx_a, goes to Alice. At Block B, Alice has an asset balance of 100 ETH;
- A 51% attack occurs at Block C, meaning that the attacker now has the ability to push through their own proposed blocks, reject blocks proposed by the other 49% of miners, and rollback blocks;
- A transaction at Block D, called Tx_b, sends Alice 50 ETH. Alice now has an asset balance of 150 ETH.
Since the 51% attack occurred at Block C, Alice’s balance of 150 ETH is not guaranteed. The attacker has the ability to rollback Block D and can therefore revert the transaction Tx_b.
This means that in the case of a 51% attack, a blockchain will be unable to maintain some of its guarantees, and a loss of funds can occur if the transactions occur after the attacker compromises the blockchain.
[Editor’s Note: As Redditor u/georgesdib said when commenting on this thread from Vitalik, ‘the likelihood of Bitcoin or Ethereum getting a 51% attack are very slim.’ And let’s face it, while Wanchain and many others offer bridges to many chains, most users are trying to bridge away from ETH and its high gas fees.]
This, however, is an admittedly small detail. The important question is whether or not cross-chain bridges, by their very nature, aggravate the impact of a 51% attack. In other words, must cross-chain bridges make 51% attacks worse?
How a 51% attack impacts a cross-chain system
For the purpose of this conversation, a cross-chain system is the combination of one or many blockchains, one or many smart contracts, and a platform that allows for the transfer of assets, messages, or even commands from one chain (the source) to another chain (the target). For simplicity, the components of a cross-chain system are as follows:
- One or many smart contracts handling cross-chain transactions on Blockchain A (source)
- One or many smart contracts handling cross-chain transactions on Blockchain B (target)
- A set of Bridge Nodes that monitor events on Blockchain A (source) and Blockchain B (target).
As specific events occur on either Blockchain A (source) or Blockchain B (target), corresponding actions happen on the other chain by the Bridge Nodes. In other words, when the Bridge Nodes detect a particular event on Blockchain A (source), they trigger an action on Blockchain B (target). You can guarantee cross-chain transactions either by atomic swaps or through Bridge Nodes using secure mechanisms such as multiparty computing (MPC).
Mr. Buterin posits that a 51% attack in a cross-chain system would be more severe than in a single-blockchain system. In his own words:
“Now, imagine what happens if you move 100 ETH onto a bridge on Solana to get 100 Solana-WETH, and then Ethereum gets 51% attacked. The attacker deposited a bunch of their own ETH into Solana-WETH and then reverted that transaction on the Ethereum side as soon as the Solana side confirmed it. The Solana-WETH contract is now no longer fully backed, and perhaps your 100 Solana-WETH is now only worth 60 ETH.”
Mr. Buterin’s mistake appears to be due to his assumption that cross-chain bridges cannot use over-collateralization to enhance security. It is true that several bridges, including popular options such as multichain, do not overcollateralize their cross-chain assets. But this is not a limitation of cross-chain bridges themselves. Rather, if Bridge Nodes need to deposit collateral to secure cross-chain bridges, the impact of a 51% attack on a cross-chain system will be identical to the impact on a single-blockchain system. To illustrate, we refer to Figure 2, below.
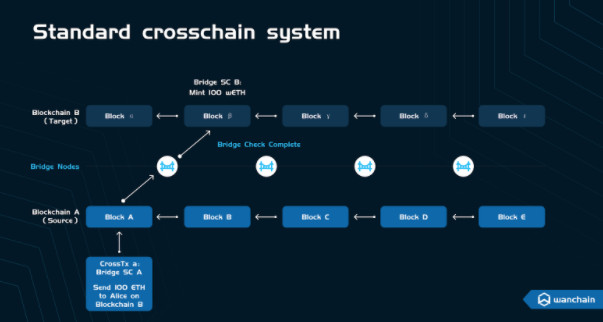
Figure 2 is a visual representation of a cross-chain system. In it, Blockchain A (source) and Blockchain B (target) connect through Bridge Nodes. At Block A on Blockchain A (source), a cross-chain transaction, called CrossTx_a, initiates a cross-chain transfer of 100 ETH to Alice’s address on Blockchain B (target). A smart contract, called “Bridge SC A” handles the cross-chain transfer by a smart contract. “Bridge SC A” locks the 100 ETH on Blockchain A (source) and then emits an event that locks the asset. The Bridge Nodes detect this event and send a request to a smart contract, called “Bridge SC B”, that mints wrapped-ETH (wETH) and sends the wETH to Alice’s address on Blockchain B (target). Before sending the mint request, the Bridge Nodes need to confirm a variety of things including:
- That the assets on Blockchain A (source) chain are locked and the block is finalized;
- That Blockchain A (source) and Blockchain B (target) are both synchronized and valid;
- That the total amount of assets that the Bridge Nodes transfer does not exceed the bridge capacity. Bridge capacity comes from the amount of staked assets in a bridge as collateral;
- That the number of Bridge Nodes that signed the transactions to mint tokens exceeds the threshold for MPC.
Let’s dissect the impact of a 51% attack on a cross-chain system. Since cross-chain transactions are more complex than regular transactions, a 51% attack also results in more complex scenarios.
[Editor’s Note: You may need to read through these examples more than once. Bridges do lots of background work that we are not necessarily aware of. But knowing how they operate can help you choose a good, secure option to bridge your assets.]
Scenario 1: A cross-chain transaction occurs before the 51% attack
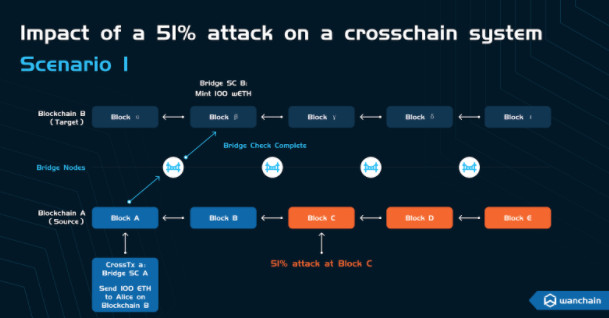
- A cross-chain transaction of 100 ETH starts at Block A on Blockchain A (source) to send 100 ETH to Alice’s address on Blockchain B (target);
- A 51% attack occurs at Block C, meaning that we have all compromised blocks and transactions issued after the attack. As we saw while dissecting Figure 1, since the cross-chain transaction, CrossTx_a, was finalized before the 51% attack, the attack does not affect it.
Scenario 2: A cross-chain transaction occurs after the 51% attack
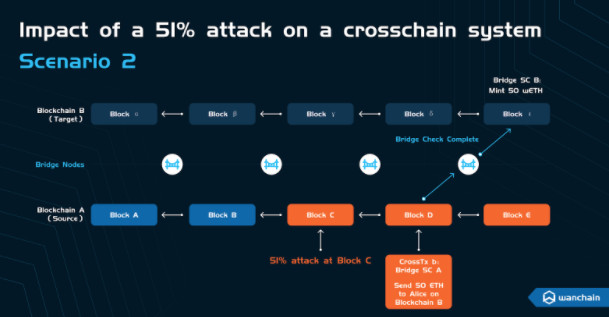
- A 51% attack occurs at Block C;
- A crosschain transaction of 50 ETH starts at Block D on Blockchain A (source) to send 50 ETH to Alice’s address on Blockchain B (target). A smart contract locks the 50 ETH called “Bridge SC A” and broadcasts the event;
-
Bridge Nodes detect the event and carry out the verification process. Here, there are two possible outcomes:
- The attacker rolls back the transactions before the Bridge Nodes complete the verification process. Then, the Bridge Nodes will detect the discrepancy and will not send the mint request on Blockchain B (target). In this case, there is no additional security risk or damage caused by the cross-chain bridge.
- The Bridge Nodes complete verification before the attacker rolls back the transactions on Blockchain A (source). Then, the Bridge Nodes issue a mint request, and wETH goes to Alice’s address on Blockchain B (target). This is the outcome of interest.
When Blockchain A (source) rolls back to Block B, prior to the 51% attack, it is again in a healthy state. And what happens if the minted asset (wETH) on Blockchain B (target) has already been spent and cannot be recovered? The Bridge Nodes trigger a compensation process using the staked collateral (the Bridge Capacity).
Rather than point out a fundamental security limitation inherent to cross-chain bridges themselves, Mr. Buterin highlighted the vital importance of having overcollateralized cross-chain bridges. Cross-chain bridges must require Bridge Nodes to deposit collateral as it is precisely this collateral that secures cross-chain transactions. This ensures that the impact of 51% attacks is not any more serious than if they occur in a single-blockchain system.
 altcoinbuzz.io
altcoinbuzz.io